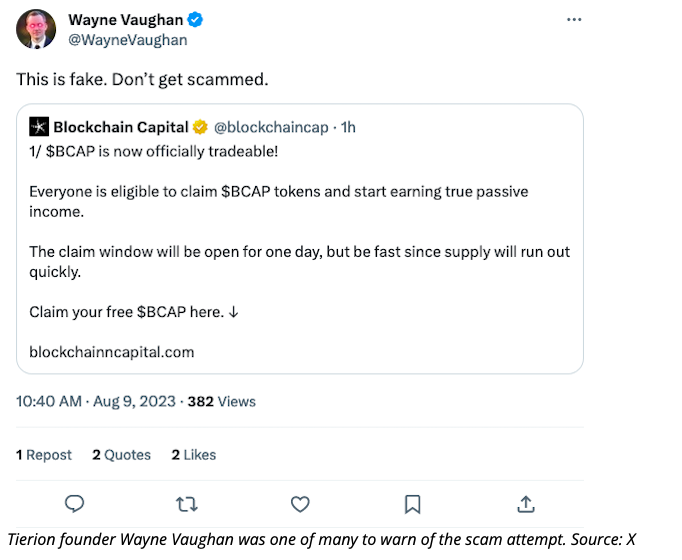
Scammers appeared to have seized control of Blockchain Capital’s crypto-centric venture capital firm’s Twitter account, X, in an effort to entice users with the allure of a token claim.
On August 9th, the compromised account issued several messages pledging a distribution of “BCAP” tokens, leading users to a counterfeit website mimicking the authentic look of the VC firm’s original platform.
Subsequently, Blockchain Capital managed to reclaim authority over the account and eliminated the fraudulent posts.

The mimicry website, employing a slight alteration in the URL by adding an extra “n” to closely resemble the authentic version, prompts users to link their cryptocurrency wallet. This technique is commonly employed by phishing scammers to deceive users into authorizing a harmful transaction that results in fund depletion.
To enhance their scheme, the scammers strategically disabled the comments section on the posts, aiming to hinder any alerts from other users regarding the potential scam. Despite this, numerous X users managed to share the posts as a cautionary measure against the scam endeavor.
Following the takeover of Blockchain Capital’s compromised account, this incident closely follows a recent FBI cautionary notice concerning criminal actors seizing control of social media profiles belonging to prominent figures within the cryptocurrency realm. Their intent is to redirect users to fraudulent imposter websites.
Additionally, a surge of deceptive posts emerged on Jeremy Hogan’s infiltrated X account, a prominent lawyer advocating for XRP. For approximately four days, these posts contained harmful links that purportedly led to an XRP giveaway.
In the latter part of July, Changpeng “CZ” Zhao, the CEO of Binance, issued a warning to his substantial 8.5 million followers on X regarding the escalating frequency of phishing attacks. This advisory came in the wake of the hacking incident involving Uniswap founder Hayden Adams’ X account.
Zhao suggested refraining from relying on text message-based two-factor authentication and instead emphasized the use of hardware devices as a more secure alternative.